Unisys Adds Kubernetes Support to Zero Trust Network Overlay
Unisys has added support for Kubernetes to a zero trust network overlay dubbed Stealth.
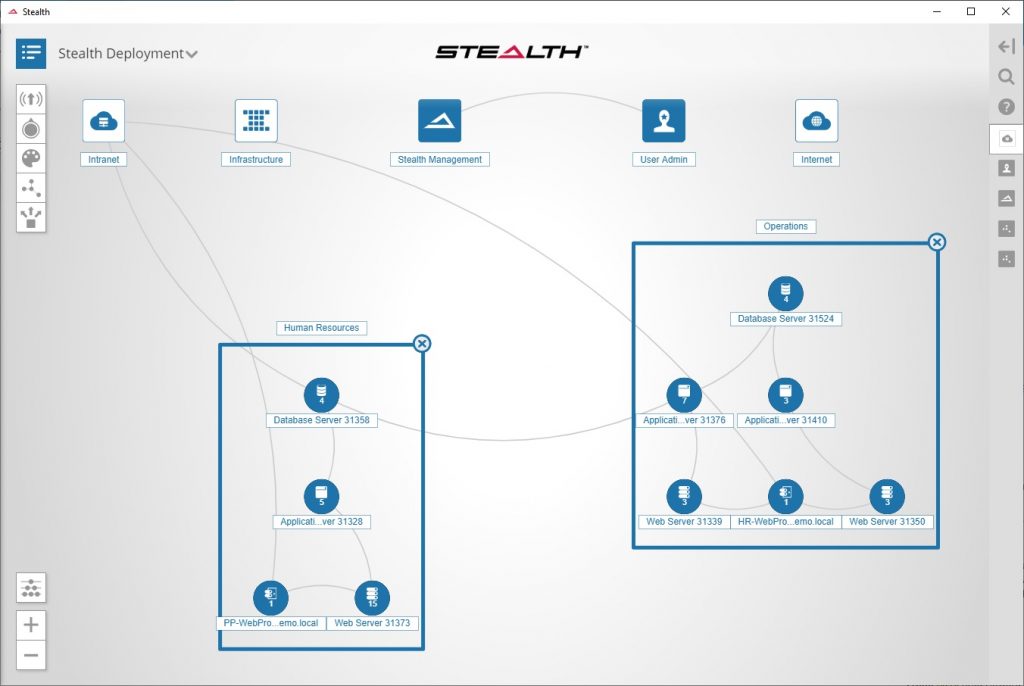
Stealth allows IT organizations to microsegment network traffic based on identity. Each encrypted microsegment becomes associated with what are known as communities of interest (COIs) through which communications are whitelisted.
In addition to adding support for Kubernetes, version 5.0 of Stealth adds enhanced support for virtual gateways that can be deployed on a public cloud, expanded application program interface (API) and automation capabilities, and the ability to isolate endpoints in as little as 10 seconds at the first sign of malware.
Vishal Gupta, senior vice president for technology and CTO for Unisys, says more organizations are looking for not only the core technology required to secure a modern IT environment but also organizations that have the expertise required to implement and manage them on their behalf.
Zero trust network overlays require a lot of expertise to implement, especially in IT environments where hundreds of microservices running across multiple Kubernetes are constantly communicating via APIs. Add in the need to integrate with monolithic applications running on legacy platforms and it becomes apparent traditional network underlays are simply not agile enough. Keeping pace with organizations that have adopted DevOps will require a more agile approach to network management that also serves to improve the overall security posture of the organization.
These days, however, there is no shortage of zero trust overlay network options. The real challenge is blending the cultures of the network operations teams and DevOps teams while simultaneously transitioning to a software-defined approach to networking.
On the plus side, awareness of the need for zero trust networks is getting a boost from the National Institute of Standards and Technology (NIST), which just made available for public comment a document that attempts to define a zero trust architecture. Overall, Alexa Reports, a market research firm, expects demand for zero trust networks to increase at a rate of more than 18% on a compound annual basis through 2026.
Naturally, there will be a high correlation between the adoption of zero trust network overlays and Kubernetes clusters. As a hyperconverged platform, Kubernetes manages network connections within a cluster. However, all network connections made between clusters need to be managed via some sort of network overlay or underlay. Less clear is to what degree dedicated networking teams will continue to manage overlays and even underlays or subsumed into larger DevOps teams. Conversely, some organizations may opt to rely on external managed service providers (MSPs) to manage both Kubernetes clusters and all the networks associated.
It may be a while before all those IT operational issues are completely ironed out. In the meantime, the paradox is that IT is becoming both more complex and agile. For example, thanks to network overlays, it now doesn’t take weeks to provision network resources. However, it’s more challenging to deploy and set up overlays and underlays in a way that makes networking truly agile. Add on top of that Kubernetes clusters and serverless computing frameworks and it becomes clear IT now consists of multiple abstractions being deployed on top of one another.