Trend Micro Extends Container Security Reach
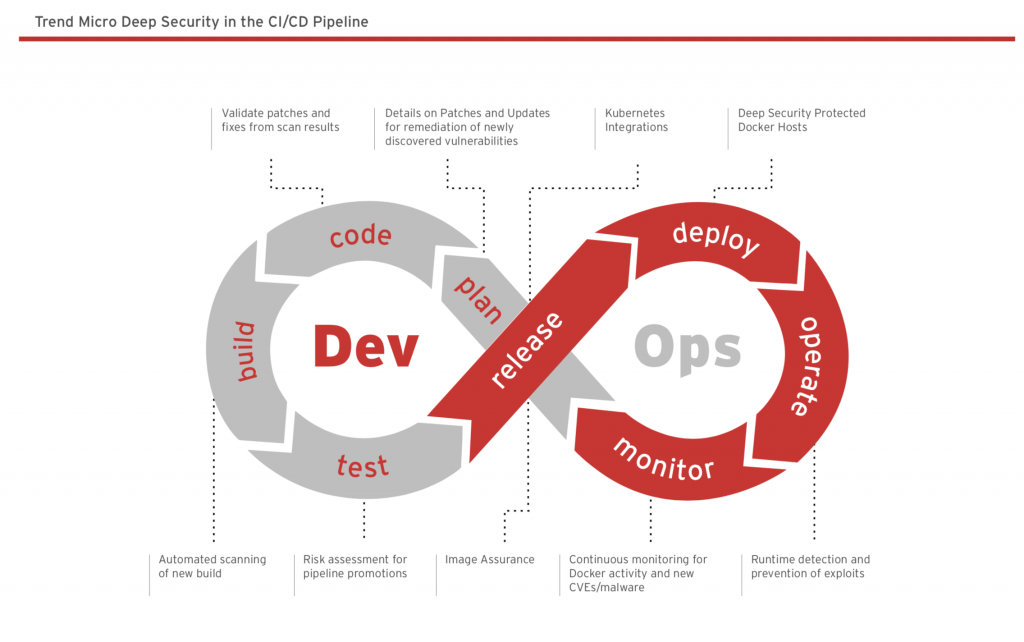
Trend Micro is extending the reach of its container security offerings to now address the full range of the DevSecOps life cycle.
The latest updates to Trend Micro Deep Security add the ability to inspect all lateral and horizontal traffic movement between containers and platform layers such as Kubernetes and Docker.
Trend Micro is also now making it possible to employ any command shell to invoke its REST application program interfaces (APIs). Those new REST APIs are intended to make it easier to automate security operating across both container orchestration tools and runtime environments.
 Additionally, Trend Micro has added support for scanning of images prior to being loaded into a container registry. Previously, Trend Micro Deep Security only scanned container images stored within a registry.
Additionally, Trend Micro has added support for scanning of images prior to being loaded into a container registry. Previously, Trend Micro Deep Security only scanned container images stored within a registry.
Finally, Trend Micro Deep Security will now also scan for embedded secrets such as passwords and private keys and provide compliance and configuration validation checks, along with image assertion for digitally signed images.
Mark Nunnikhoven, vice president of cloud research for Trend Micro’s VP of cloud research, says the rise of containers is now driving a massive wave of innovation across the cybersecurity sector. In addition to dealing with the fundamental ephemeral nature of containers, the platforms used to secure them need to be accessible to both developers and cybersecurity professionals, he says.
Developers increasingly are expected to make sure containers are secure as part of the quality control process. However, after containers are deployed, cybersecurity professionals need to be able to inspect them to make sure no insecure code may have been accidentally or maliciously included.
The fundamental challenge organizations face today is finding a way to make sure cybersecurity policies are enforced without slowing down the application development process. Achieving that goal requires developers and cybersecurity teams to work past a lot of animosity that has built up over the years. Cybersecurity professionals, however, have little alternative to patching things up with developers, given the chronic shortage of cybersecurity professionals. Unless developers take more responsibility for implementing cybersecurity controls, there is no way cybersecurity professionals will be able to keep pace with the rate at which modern applications are now being deployed and updated.
Nunnikhoven says Trend Micro’s contribution to enabling that rapprochement is to focus more on container cybersecurity life cycle management, which includes a REST API that developers can invoke easily.
Like most cybersecurity vendors, Trend Micro is making a case for employing a common cybersecurity framework across both modern and legacy application environments. The shift to modern cloud-native applications, however, has fostered the rise of a small army of startup cybersecurity vendors. It’s too early to say whether challengers or incumbent security vendors will carry the container security battle. However, it’s clear that when it comes to securing containers, there is no shortage of potential platforms. The challenge now is training everyone involved how to employ the best DevSecOps processes required to wield them.



