Styra Shifts Kubernetes Policy Management Left
At the KubeCon + CloudNativeCon Europe 2019 conference this week, Styra announced it has extended the policy management engine it created for Kubernetes clusters to provide additional integrations and controls intended to advance best DevSecOps practices.
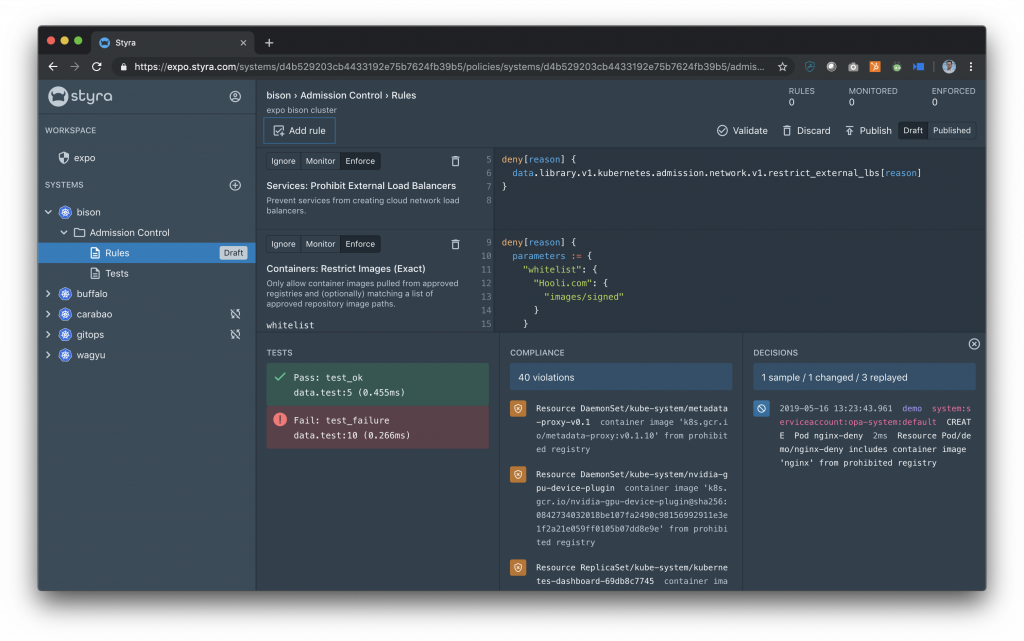
The Styra Declarative Authorization Service (DAS) is based on the open source Open Policy Agent (OPA) software the company developed. The latest edition adds support for Git to make compliance a natural extension of a GitOps process, as well as Policy Check for GitHub Apps and a command line interface (CLI) for implementing policy checks with a continuous integration/continuous delivery (CI/CD) pipeline. Cybersecurity policies via either an API or CLI now can be saved to a Git repository.
CLI support is complementary to existing Styra application programming interfaces (APIs) that enable users to run policy checks against a local Git repository and stop the pipeline from advancing if failures exist. Information about the failures is then provided to developers to close the DevSecOps loop.
 Chris Webber, vice president of marketing for Styra, says the goal is to enable DevOps teams that have embraced Kubernetes to manage compliance as code along with the rest of the IT environment. Providing that capability is critical because a lack of visibility into Kubernetes security and compliance policies is now the major inhibitor to Kubernetes adoption in the enterprise, he says. Most enterprise IT organizations have deployed one or two Kubernetes clusters; however, large-scale deployment of Kubernetes won’t occur until developers can show how they have met the same cybersecurity and compliance mandates that apply to every other platform, he adds.
Chris Webber, vice president of marketing for Styra, says the goal is to enable DevOps teams that have embraced Kubernetes to manage compliance as code along with the rest of the IT environment. Providing that capability is critical because a lack of visibility into Kubernetes security and compliance policies is now the major inhibitor to Kubernetes adoption in the enterprise, he says. Most enterprise IT organizations have deployed one or two Kubernetes clusters; however, large-scale deployment of Kubernetes won’t occur until developers can show how they have met the same cybersecurity and compliance mandates that apply to every other platform, he adds.
Given the chronic shortage of cybersecurity experts, the onus for providing that layer of security on emerging platforms such as Kubernetes is now clearly shifting left toward developers, Webber notes. In fact, the adoption of Kubernetes as a platform for running cloud-native applications based on containers inevitably will force the DevSecOps issue within organizations large and small.
It’s not clear the degree to which cybersecurity professionals will endorse that transition, as many of them don’t trust developers. To put the minds of cybersecurity professionals more at ease, Styra DAS supports role-based access as well as single sign-on capabilities enabled via support for OpenID Connect, including time-of-day access, two-factor authentication, complex passwords and other controls.
Styra also provides user activity logs and activity from API calls and system events that create, delete, update or modify a resource using a custom verb. All log entries record the request and response data of the API actions performed.
Many developers have been able to stay under the cybersecurity and compliance radar when it comes to deploying applications on Kubernetes clusters. It is only a matter of time, however, before cybersecurity and compliance teams discover those clusters. Rather than waiting for an inevitable discussion that likely will go badly, many DevOps teams that have embraced Kubernetes might want to consider getting in front of the security and compliance controls now that developers know they eventually will be asked to put in place anyway.




