StackRox Makes Securing Kubernetes Easier
StackRox today added a raft of tools to its container security platform designed to make it easier to secure Kubernetes clusters.
Version 2.5 of the StackRox Kubernetes Security Platform adds additional deployment and runtime controls that enable organizations to enforce security controls to improve vulnerability management, network segmentation, configuration management and threat detection.
Wei Lien Dang, vice president of product at StackRox, says organizations deploying multiple Kubernetes clusters are now looking for ways to streamline security management across Kubernetes clusters in on-premises IT environments and public clouds that likely are based on different distributions of Kubernetes.
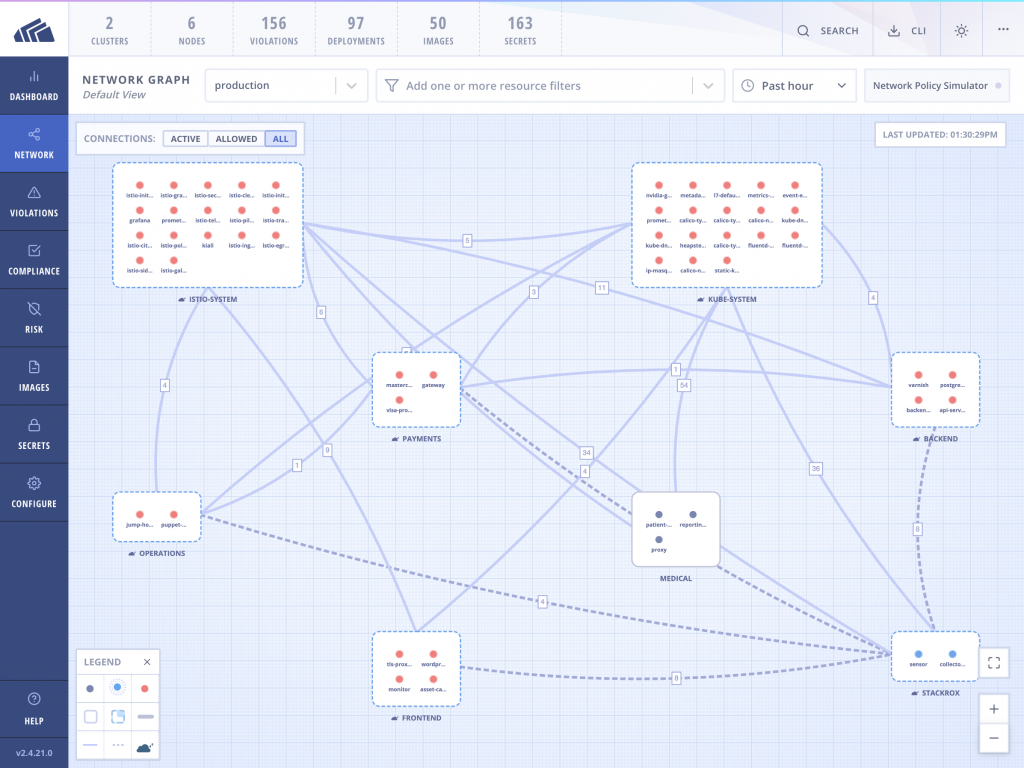
The latest version of the StackRox container security platform automatically baselines network activity, identifies allowed but unnecessary network connectivity and updates Kubernetes network policies to achieve more secure network configurations using a Kubernetes Network Policy Generator.
StackRox also nows employing machine learning algorithms to baseline process activity within containers that IT teams can either apply controls to at runtime or selectively whitelist.
StackRox also has added dynamic admission control to prevent the deployment of containers based on preconfigured or custom policies. The platform now can limit access to specific Kubernetes components such as namespaces in addition to analyzing user and service account privileges against potential misconfigurations, identifying best practice violations, performing risk assessments and ensuring compliance with industry standards and custom policies.
Finally, StackRox Kubernetes Security Platform now includes additional features for customers deploying Kubernetes in air-gapped networks with no internet connectivity to provide custom security notices, offline vulnerability definition updates and a streamlined setup and deployment process.
As a container security platform focused exclusively on securing containerized applications running on a Kubernetes cluster, StackRox expects to become the preferred platform for organizations embracing more flexible DevSecOps processes within hybrid cloud-native computing environments, Dang says. Larger cybersecurity rivals are more focused on trying to extend approaches to enforcing cybersecurity policies developed for more rigid legacy monolithic application environments, he says.
The challenge is cybersecurity teams are not all that excited about having to develop and manage separate cybersecurity policies just for containerized applications. In fact, that lack of enthusiasm is slowing the deployment of containerized applications in production environments.
It’s not clear yet to what degree of influence developers or cybersecurity teams will exercise over the decision to acquire a container security platform. There’s no doubt responsibility for cybersecurity is shifted further left on to the shoulders of developers as they implement policies defined by cybersecurity professionals. However, that doesn’t mean developers are selecting the cybersecurity platform that enables that shift. Rather, savvy developers are engaging cybersecurity teams more proactively to make sure they gain access to the tools needed to achieve what has become a more common goal. What is certain is developers via application programming interfaces (APIs) will be interacting with container security platforms a whole lot more than they ever did with legacy security platforms that, for the most part, are still managed using graphical user interfaces.