CNCF Moves Falco Kubernetes Security Platform Forward
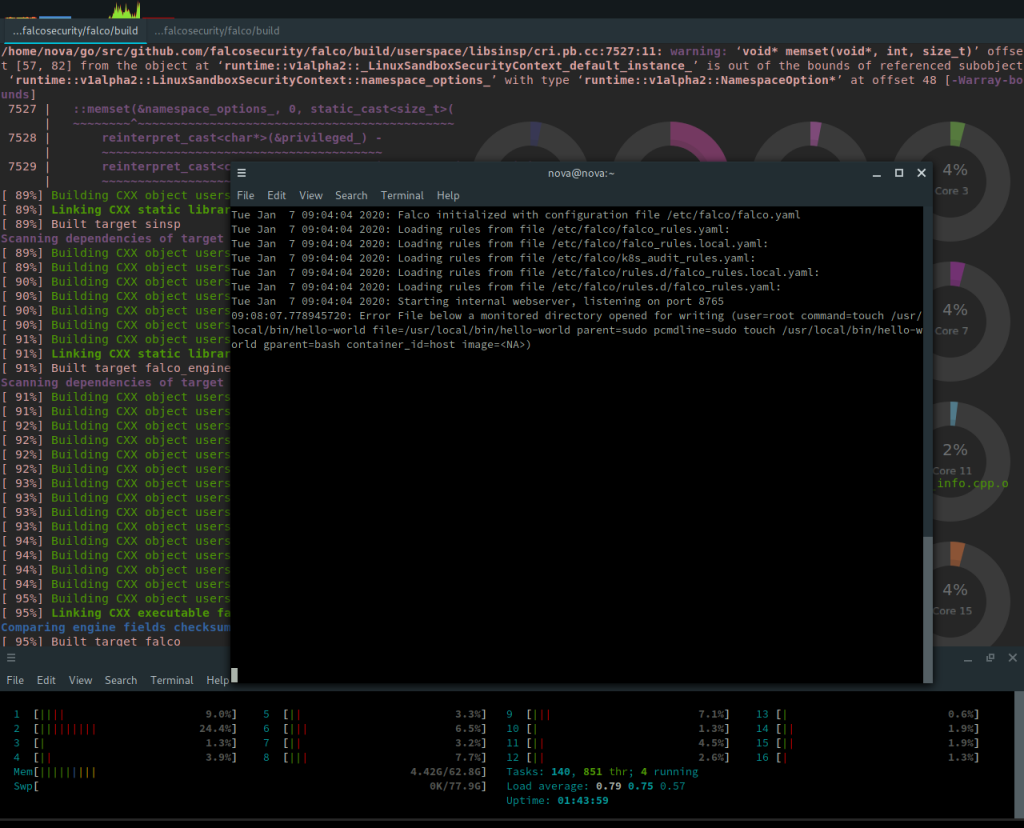
The Cloud Native Computing Foundation (CNCF) announced today it has advanced the open source Falco project for securing Kubernetes runtime environments using an intrusion and abnormality detection tool. Falco employs the Extended Berkeley Packet Filter (eBPF) to capture system calls and integrate with Kubernetes application programming interfaces (APIs) to provide visibility into Kubernetes runtime environments.
Potential issues Falco can surface include new and unpatched vulnerabilities, insecure configurations, leaked or weak credentials and potential insider threats.
Sysdig founder and CTO Loris Degioanni says Falco as an incubation-level project is only one level away from graduation. Falco has been downloaded more than 8.5 million times, representing a 257% increase since becoming a CNCF project, he says.
As developers take on more responsibility for application security as part of the growing shift toward DevSecOps, many of them are showing a preference for open source software that doesn’t require developers to get a purchase order approved to employ. In addition to Falco, the open source Clair software for scanning containers is starting to gain traction among DevSecOps teams, which Degioanni says is a perfect complement to Falco.
Developed by Sysdig, Falco counts 55 contributors from companies including Frame.io, Shopify, Snap and Booz Allen Hamilton to the project. A governance model was defined last year, and Falco is available in the Google marketplace. It also is included in Amazon Web Services (AWS) Firelens, a log router for its Elastic Container Service (ECS), and Google Anthos, a cloud framework based on Kubernetes. Sysdig also provides support for Falco within a namesake monitoring platform that can support all the environments on which Kubernetes might be deployed, adds Degioanni.
The Falco community has also created Operator software that makes Falco simpler to deploy on a Kubernetes cluster. What’s more, Sysdig recently launched a Cloud-Native Security Hub, a repository for discovering and sharing Kubernetes security best practices and configurations. That hub currently hosts Falco rules that Sysdig hopes the community will expand upon to include rules and configurations for other Kubernetes security tools.
As part of that goal, Falco is transitioning to an “API first” architecture to enable the community to begin developing integrations with other platforms and tools, including Prometheus, Envoy and Kubernetes. In addition, those APIs soon will be encrypted, notes Degioanni.
There are, of course, now a lot of choices when it comes to container security platforms. It remains to be seen to what degree IT organizations will prefer to rely on open source versus proprietary platforms. Nor is it absolutely clear to what degree DevOps teams versus cybersecurity professionals might make that decision. The one thing that is certain is now that more production workloads are starting to be deployed on Kubernetes, making sure the platform is secure has become a higher priority. The challenge IT organizations will face is first determining the right set of tools and then defining the best DevSecOps practices required to achieve that goal.