Aqua Security: More Platforms Add Trivy Container Scanning Tool
Aqua Security today revealed that its open source Trivy container scanning software is now available by default in a growing number of container platforms.
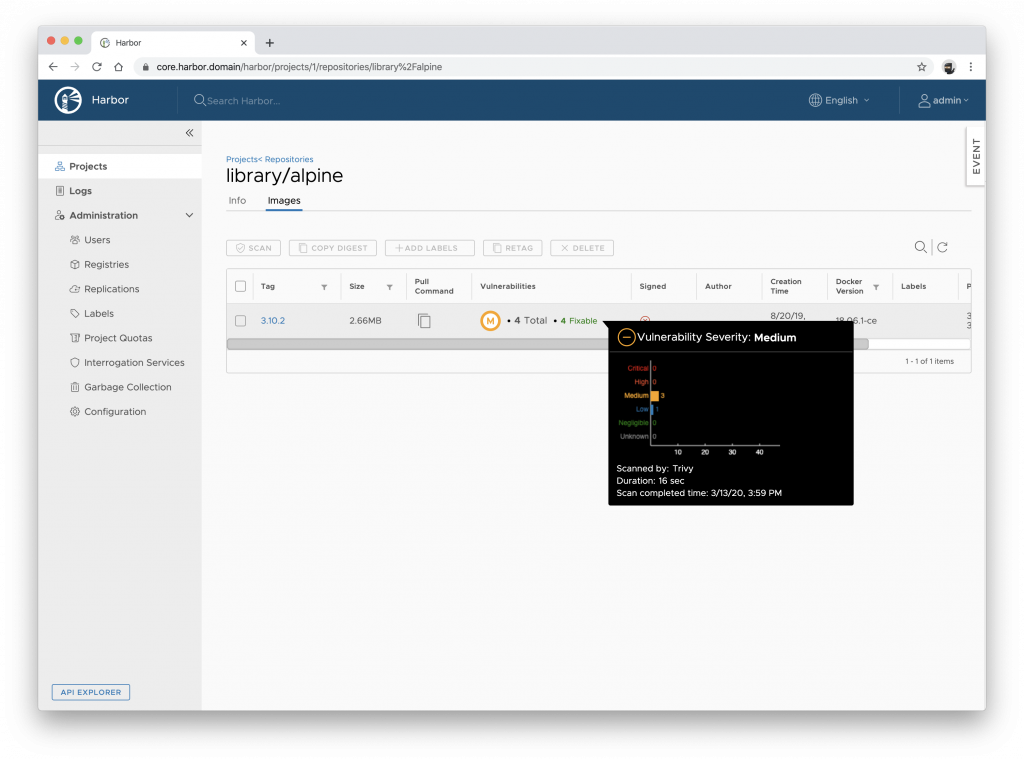
Currently available under a royalty-free Apache 2 license, Trivy will be included as the default scanner in Harbor, an open source container image registry project under the Cloud Native Computing Foundation (CNCF), as well as the registry from Docker Inc. and the Mirantis Docker Enterprise platform, which was previously owned by Docker Inc.
Liz Rice, vice president of open source engineering at Aqua Security and chair of the CNCF Technical Oversight Committee, says integrating Trivy within a registry or container platform advances DevSecOps because the ability to scan containers becomes that much easier for developers to run while accessing containers.
That approach also helps developers view cybersecurity as being something less than a black art that someone else should handle, she adds.
As a project, Trivy is only 10 months old. Nevertheless, Rice contends it matches or exceeds the capabilities of other container scanning software with the possible exception of not being integrated with any commercial threat intelligence service. Trivy is integrated only with open threat intelligence platforms that are available for free. However, individual cybersecurity teams can integrate Trivy with any DevOps platform or service on their own.
It will be interesting to see what impact the availability of free container scanning software embedded within various container platforms will have on the demand for commercial container scanning software. Cybersecurity vendors in many cases already have made container scanning tools available as part of a larger container security platform, so in one way or another container security software is already available for a nominal cost. The challenge, of course, is making container scanning software available in a way that can’t be ignored easily by developers because no one had to, for example, sign off on a separate purchase order.
In theory, containerized applications should be more secure than monolithic applications because it’s easier to rip and replace containers that might include vulnerable code than it is to patch an entire monolithic application. Of course, that capability only matters if some tool is employed to actually scan containers. There most likely will come a day soon when every container being loaded into a registry is scanned automatically.
In the meantime, it’s clear that responsibility for application cybersecurity is finally shifting left. Developers are increasingly being held accountable to make sure the right controls have been implemented within an application as part of the overall quality assurance process. It’s then up to cybersecurity teams to verify those controls have been properly implemented. Historically, cybersecurity teams have not trusted developers to implement those controls, while developers tended to view cybersecurity as being someone else’s responsibility. Getting developers to appreciate cybersecurity and condition cybersecurity teams to trust developers represents one of a major cultural transition in the months and years ahead that not all IT teams will be able to embrace successfully.