Zettaset Adds Kubernetes Support to Encryption Platform
Zettaset announced it has added support for Kubernetes to its software for encrypting data at rest.
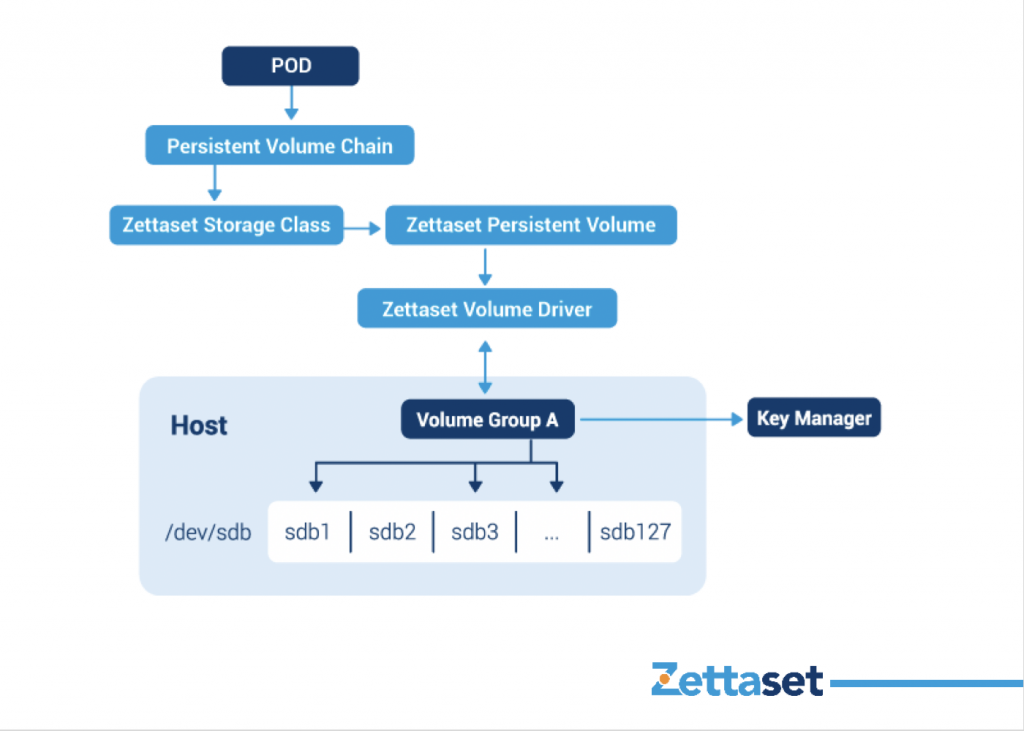
Company CEO Tim Reilly says Zettaset XCrypt Kubernetes Encryption is designed to make it easier for IT organizations that have adopted Kubernetes to centralize the management of encrypted data across multiple Kubernetes clusters. Previously, Zettaset had enabled the data stored on physical storage systems by Docker containers to be encrypted at rest.
That approach makes it possible to now automate encryption policy management as part of a larger DevSecOps initiative, adds Reilly. Given the fluid nature of the way containers move across platforms, a centralized approach to applying encryption across multiple Kubernetes clusters is now essential, he says.
Zettaset XCrypt Kubernetes Encryption is designed to be an extension to the Kubernetes Secrets encryption capabilities already included in the base distribution of Kubernetes. It encrypts data at rest, while Kubernetes Secrets protects tokens and passwords.
Reilly says it is clear cybersecurity concerns are one of the primary issues limiting the adoption of Kubernetes clusters in enterprise IT environments. Many of the monolithic applications relied on today by enterprise IT organizations are encrypted, so if application developers want to replace those applications they need to find a way to encrypt the data being accessed by microservices-based applications deployed on Kubernetes clusters, he notes.
Zettaset has been making the case for a software-defined approach to encryption that makes it easier for IT teams to encrypt everything. Historically, many organizations have relied on hardware-based encryption largely because of concerns over the impact encryption might have on application performance. Zettaset claims its software-based approach based on Advanced Encryption Standard (AES) 256-bit encryption adds minimal latency to any application accessing encrypted data.
In the months ahead many organizations will begin either updating or replacing the encryption engines currently employed within legacy applications because of the rise of quantum computing. The concern is nation-states soon will have enough compute power to easily crack the algorithms employed to encrypt data. IT teams will have to decide whether they want to replace the encryption engines in those applications or develop an entirely new application. However, replacing an encryption engine in a monolithic application may prove more time-consuming than replacing it with a modern microservices-based application running on Kubernetes.
Whatever the outcome, encryption use is gaining, thanks in part to the rise of the Encrypt Everything movement being led by Amazon Web Services (AWS). As the cost of compute horsepower continues to decline, concerns about the cost and application performance overhead that historically has limited encryption adoption are starting to fade. The only remaining challenge is managing all the encryption keys that are generated by each microservice. That issue is mitigated by centralizing the management of encryption keys using Zettaset XCrypt Kubernetes Encryption, says Reilly.
It’s not clear to what degree responsibility for encrypting data will shift left toward developers within the context of a DevSecOps process. However, the more encryption becomes software-defined, the easier it becomes to make the encryption of data a natural extension of any DevOps pipeline.