Sophos Adds Ability to Scan Container Images
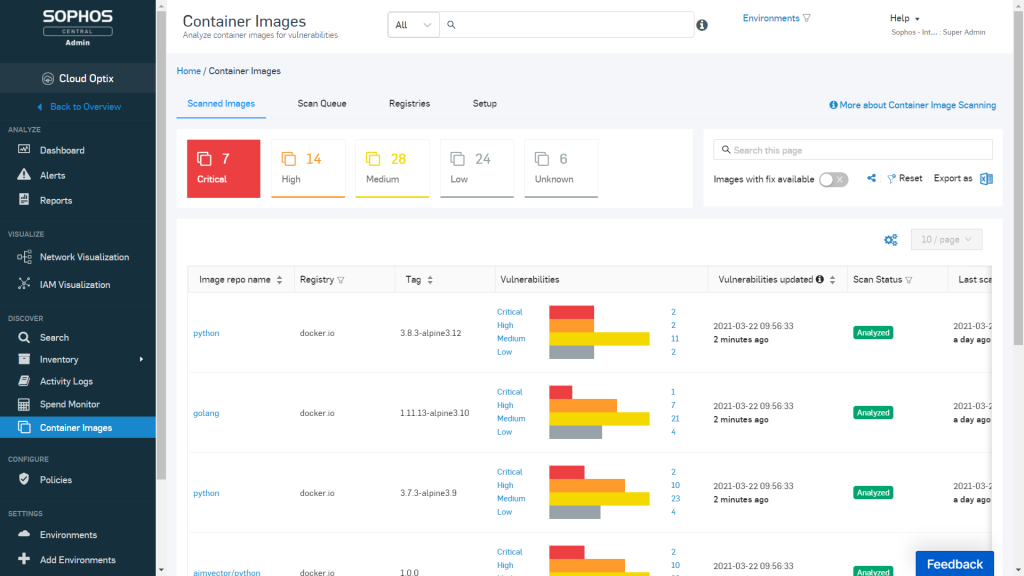
Sophos this week announced it is extending its Cloud Optix service for cloud security posture management (CSPM) to include support for container image scanning.
Richard Beckett, senior product marketing manager for public clouds at Sophos, says that as cloud computing expands to include new classes of applications, IT teams will need a common framework for applying security policies to both existing monolithic applications as well as container- and microservices-based applications now emerging in production environments.
Cloud Optix now makes it possible to scan container images for operating system vulnerabilities both before and after they are deployed. It also identifies ways to remediate those issues as quickly as possible, Beckett adds. As a software-as-a-service (SaaS) platform, Beckett says Cloud Optix also eliminates the need to rely on agent software to scan container images.
Currently, Cloud Optix supports Amazon Elastic Container Registries (ECR), Microsoft Azure Container Registries (ACR), Docker Hub registries, Bitbucket and GitHub as well as images in build pipelines they can scan using the Cloud Optix application programming interface (API).
Beckett says as IT becomes more complex, organizations are relying more on cloud platforms to manage cybersecurity. That approach not only makes it easier to centralize the management of cybersecurity across multiple platforms, it enables cybersecurity teams to work from anywhere, Beckett says. Most organizations will not want to acquire a separate security platform for each type of application environment they need to support, he adds.
Those cloud platforms also make it feasible to aggregate enough data to apply machine learning algorithms and other forms of artificial intelligence (AI) to cybersecurity, adds Beckett.
Most of the breaches involving containers, to date, have involved cryptojacking, which many IT professionals still regard as a “victimless” crime. Cryptojacking involves bad actors siphoning small amounts of processing power to mine cryptocurrencies. However, the prevalence of cryptojacking suggests cybercriminals now understand how to compromise container environments.
That will become a more critical issue as digital business transformation initiatives lead to rollouts of more mission-critical, containerized applications that developers will rip and replace to add new functionality.
Unfortunately, far too many developers are relying on the ephemeral nature of containers for cybersecurity. The assumption is that a container is only running for a few seconds, and won’t be discovered by cybercriminals. However, the components within a container image are likely to be compromised long before they were encapsulated. It’s also worth noting that the rise of more stateful containerized applications means that containers are starting to run longer.
Regardless of how cybersecurity evolves in next era of the cloud, it’s is clear that developers will be assuming more responsibility for security as adoption of DevSecOps best practices become more widespread. In the meantime, one thing that will become more apparent is that securing monolithic applications was child’s play compared to securing a modern cloud-native computing environment.