Carbonetes Unfurls Container Security Service
Carbonetes today emerged from stealth mode to formally launch a namesake container application security testing service.
Company CEO Mike Hogan says rather than requiring IT teams to acquire and integrate disparate container security tools, it’s become apparent that allowing developers to leverage a cloud service is just going to be fundamentally more efficient.
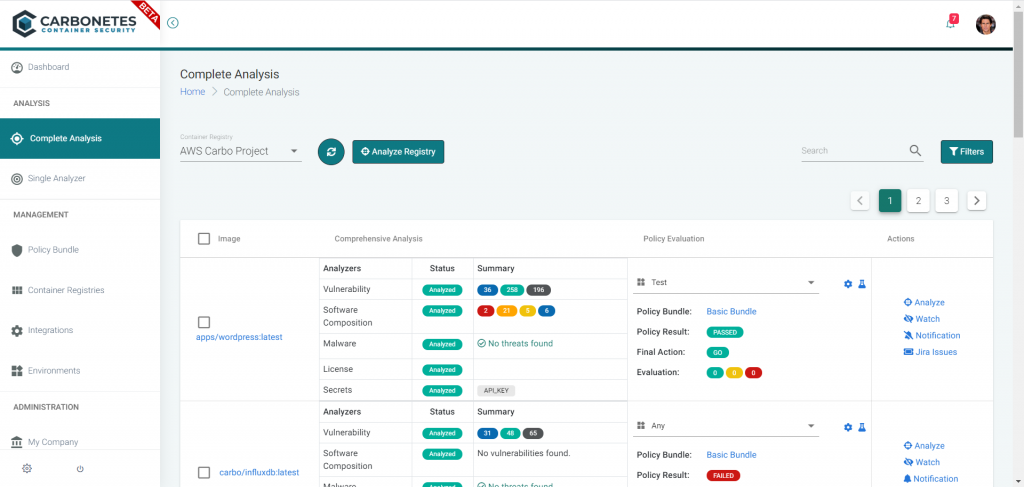
The Carbonetes service not only provides tools to identify malware hidden in the container, but there are additional tools to surface open source vulnerabilities, licenses and dependencies as well as vulnerabilities and potential secrets issues in the code that has been embedded in a container.
Hogan says Carbonetes is able to achieve that goal by taking advantage of Kubernetes to run all these processes in parallel. Carbonetes will launch pods in parallel to provide results in 1% of the time it would take to achieve the same goal using existing approaches to container security, he says.
In addition, Carbonetes makes available a plug-in that makes it possible to invoke its service as a natural extension of the Jenkins continuous integration/continuous delivery (CI/CD) platform, Hogan adds.
Organizations can also leverage the Carbonetes service to create, edit, test and managing security policies. Analysis results are then evaluated against those policies to recommend the most appropriate action, says Hogan. That approach allows developers to address security issues long before anyone on a cybersecurity team ever knew they might have existed.
One of the primary benefits of containers is they accelerate the rate at which software can be developed. The downside of that acceleration is the number of opportunities for malware and vulnerabilities to be introduced into applications increases as the number of containers being deployed rises. Before too long, the rate at which applications are being developed and deployed starts to slow as the number of container images that need to be scanned increases.
As a cloud service designed from the ground up to address that issues, Hogan notes Carbonetes enables IT teams to embrace DevSecOps processes without having to significantly slow down the rate at which container applications are being developed and deployed.
At the same time, the Carbonetes service eliminates the need for DevOps teams to deploy and maintain a wide range of security tools that now can be accessed as service, he adds.
In theory, applications built using containers should be more secure than monolithic applications. Containers make it easier to rip and replace modules that may contain malware or vulnerabilities. In contrast, an entire monolithic application will need to be patched every time a vulnerability is discovered. Because of the cumbersome nature of that process, it’s not uncommon for known vulnerabilities to exist in a monolithic application long after they are initially discovered. In contrast, vulnerabilities discovered in containers are regularly eliminated as part of a software development life cycle based on best DevSecOps processes.
It’s most likely only a matter of time before additional container security services become available. In the meantime, DevOps teams might want to consider to what degree they want to maintain all the tools and infrastructure required to secure containers once such services are readily available.